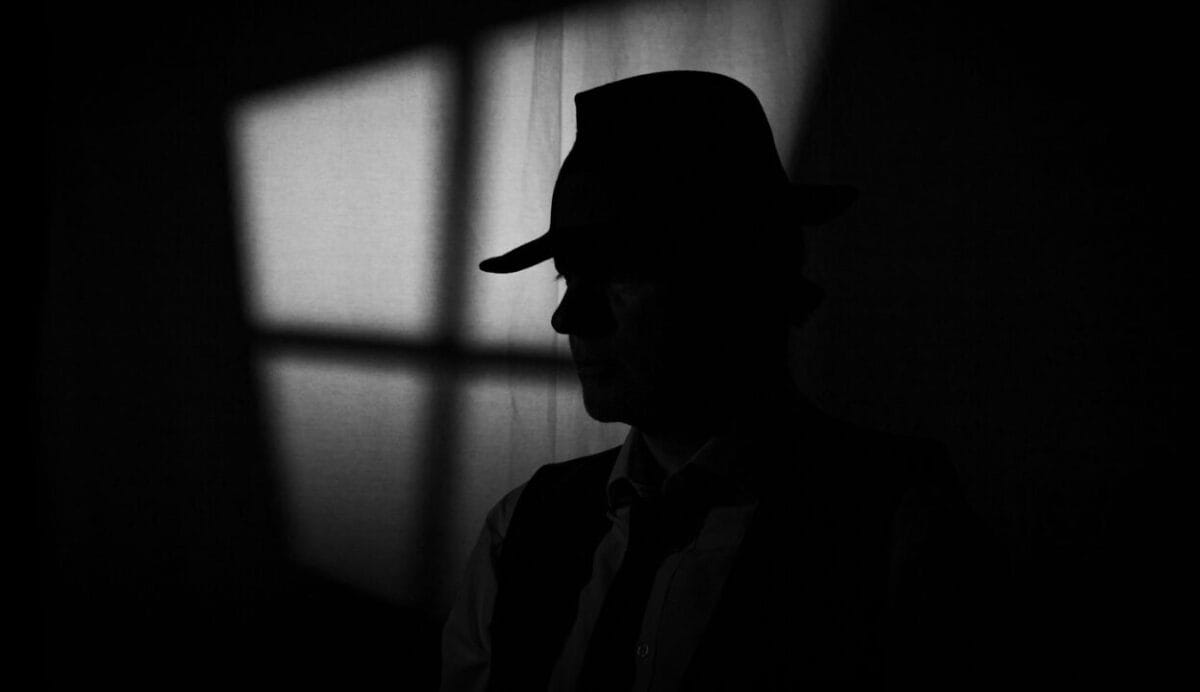
Most organisations could be hacked within half an hour according to cybersecurity specialist Michael Connory, despite promises from chief executives they take cybersecurity seriously.
Speaking at the Professional Planner Licensee Summit in Katoomba recently, Security in Depth CEO Michael Connory said most organisations across Australia are oblivious to cyber security threats.
“When we talk about policies and procedures across Australia, 93 per cent don’t have an appropriate cybersecurity policy.”
Connory said at least 95 per cent of CEOs he has spoken to will openly assure him they take cybersecurity seriously.
“I can guarantee you that we can hack 100 per cent of those organisations in about half an hour.”
Testing liability
In May, the Federal Court found RI Advice breached its licensee obligations with a lack of cybersecurity risk management systems, which ASIC described as an Australian first.
RI Advice Group CEO Peter Ornsby previously told Professional Planner client data was stolen and likely sold to the black market.
Appearing at the summit in the same session, Ornsby said the experience has been an “eye opener” for the licensee.
“We have absolute responsibility over so much more than compliant advice and that is one of the challenges of being a licensee. Where do those responsibilities start and finish? Do they go further into workplace relations? It’s pretty far reaching.”
All practices operating under the RI Advice license have now conformed to the new protocols, Ornsby said, which took about nine months of work.
“We’re about to go through another annual review of every practice and that’s happening across the networks.”
Ornsby said it was a surprise the case made it through the court system, but the outcome created a “healthy precedent”.
“It was a test case. I understand where ASIC are going with this and there’s a whole lot of merit around it as well.”
Magic words
At the summit, Connory conducted an experiment where he emulated the hotel Wi-Fi to see who would mistakenly log into it.
“We had three people attach from the group which meant we could’ve read all of their emails and all of their information,” he said.
When asked whether he read any of those emails, Connory assured moderator Simon Hoyle he did not.
Connory said it was too commonplace for people to re-use the same password or five different variations.
“They’ve got five different versions of the same password. Somebody you love, your partner, your football team, your favourite food, a date. If it has to have a capital letter it’s first and if it has to have a special character it will be an exclamation point at the end. Pretty easy to be able to guess.”
Most people will use their email address as the username, Connory said, which makes it easier for a hacker to get into a system.
“We had a look at a lot of the simple things we could do immediately to be able to help the practices evolve. We put together policies and procedures that were understandable to a small business that were easily disseminated. We had a look at their IT controls, passwords, who has access to what, what do they have access to.”
Of the 110 practices he audited, Connory said he found most had an IT provider helping them but none of them were monitoring systems for outside activity.
“We found a half a dozen organisations that people were trying to hack while going through the review.”





















Leave a Comment
You must be logged in to post a comment.